A huge thanks to Sacha Yves Saint-Leger and Joseph Schweitzer for their kind support. We appreciate your assistance.
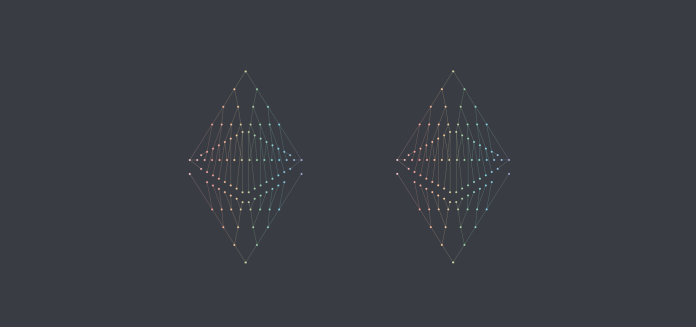
Sharding is one of the advantages that eth2 has over eth1. The concept was developed from database research. A chunk is a small part of a larger whole. In the context of databases or Eth2, it refers to the method of dividing a system’s compute and storage into smaller components and processing each one individually before combining the results. Sharding can be used with eth2 with multiple shards. This leads to significant improvements.
But eth2 also has a less known type of sharding. From a protocol design perspective, it is very exciting. Let’s look at Fragmented Consensus.
Fragmented Consensus
Network performance is influenced by the slowest node’s processing power or the fastest validator’s CPU. The resources available to one validator also limits the number of validators who can join in the consensus. At a certain point, the node with the least resources may not be able to participate since it can’t keep up with the voting. This is where eth2 comes in. It breaks down time into intervals, known as epochs.
Each 12 second period of the chain will see a new block added. These are the validators’ voting mechanisms, as well as any transactions that make it useful. Each epoch has 32 slots (6.4 minutes) in which the beacon chain does all the calculations needed to keep the chain running. This includes the justification and finalization of new blocks, as well as the awarding of penalties and rewards to validators.
Validators work together as a team to accomplish their tasks. A validator may only belong to one beacon chain or shardchain committee at a given time. Furthermore, each validator is only allowed to issue certifications once per epoch. A certification is a vote to approve the proposed beacon block in the specified slot.
The security model of eth2’s fractured consensus is built upon the idea that committees are more precise than the entire set. For example, 33% of validators could be malicious, and they might end up in one group. This could put the security model at risk.
Therefore, we must make sure that this doesn’t happen. In other words, we must make sure that 33% are honest and 33% are malicious within a committee. It turns out that this can be done by doing two things: ensuring that committees are assigned randomly and that each committee requires a minimum of two validators. With 128 randomly selected validators for each committee, it is highly unlikely that an attacker will control more than 2/3 (probability below 2-40).
It’s time to make it stop
Certifications are the ones that have been verified by an authorized party. An attestation is composed of several components, namely: voting for the head of the current beacon chain, voting on the beacon block to be justified/finalized, voting on the current state of the shard chain, and all validators must sign this agreement. By combining all these components into one attestation, the efficiency of the system is increased.
<